锤子
绕过安全引导在智能手机上进行激光故障注入(错误注入)
- 类别:课件讲义
- 上传人:聚擘
- 上传时间:2017/11/15 14:25:23
- 文件大小:3798K
- 下载次数:2
-
消耗积分 : 免积分
简介:
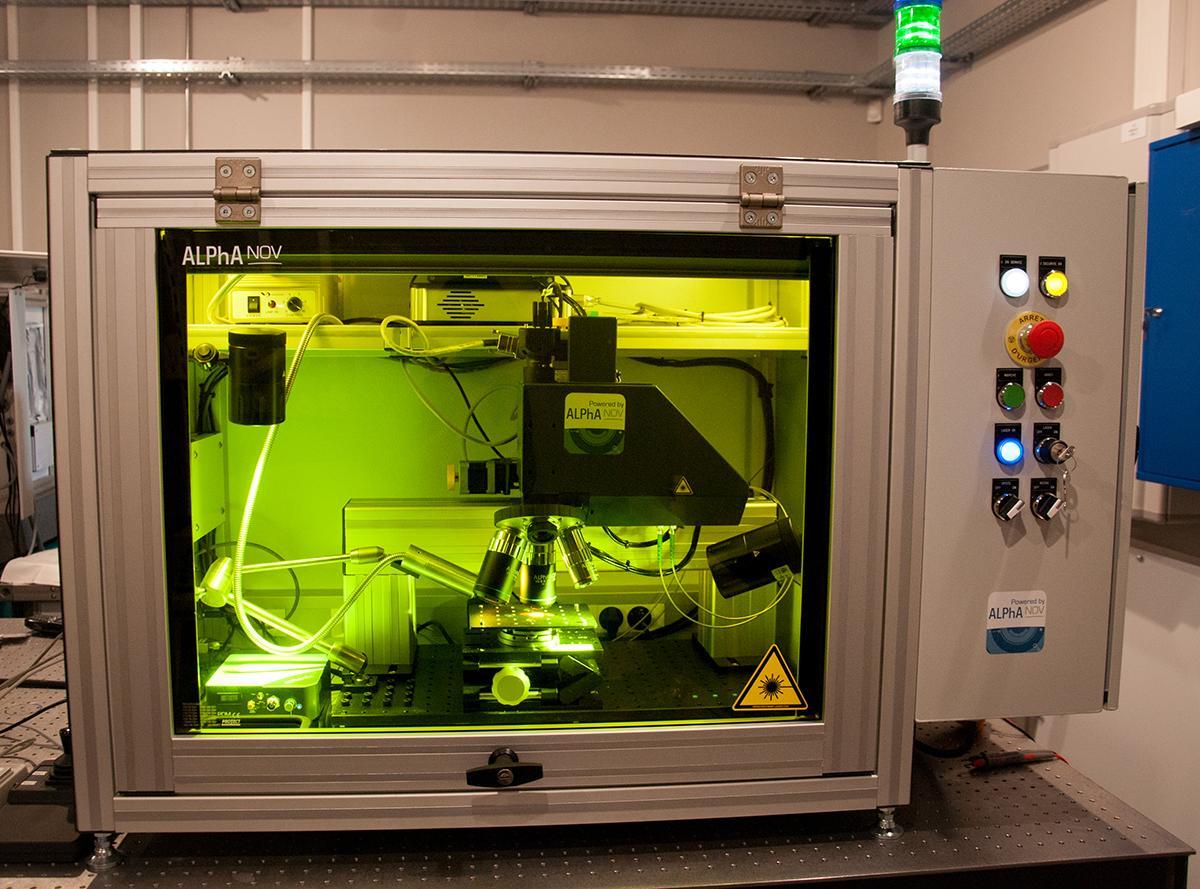
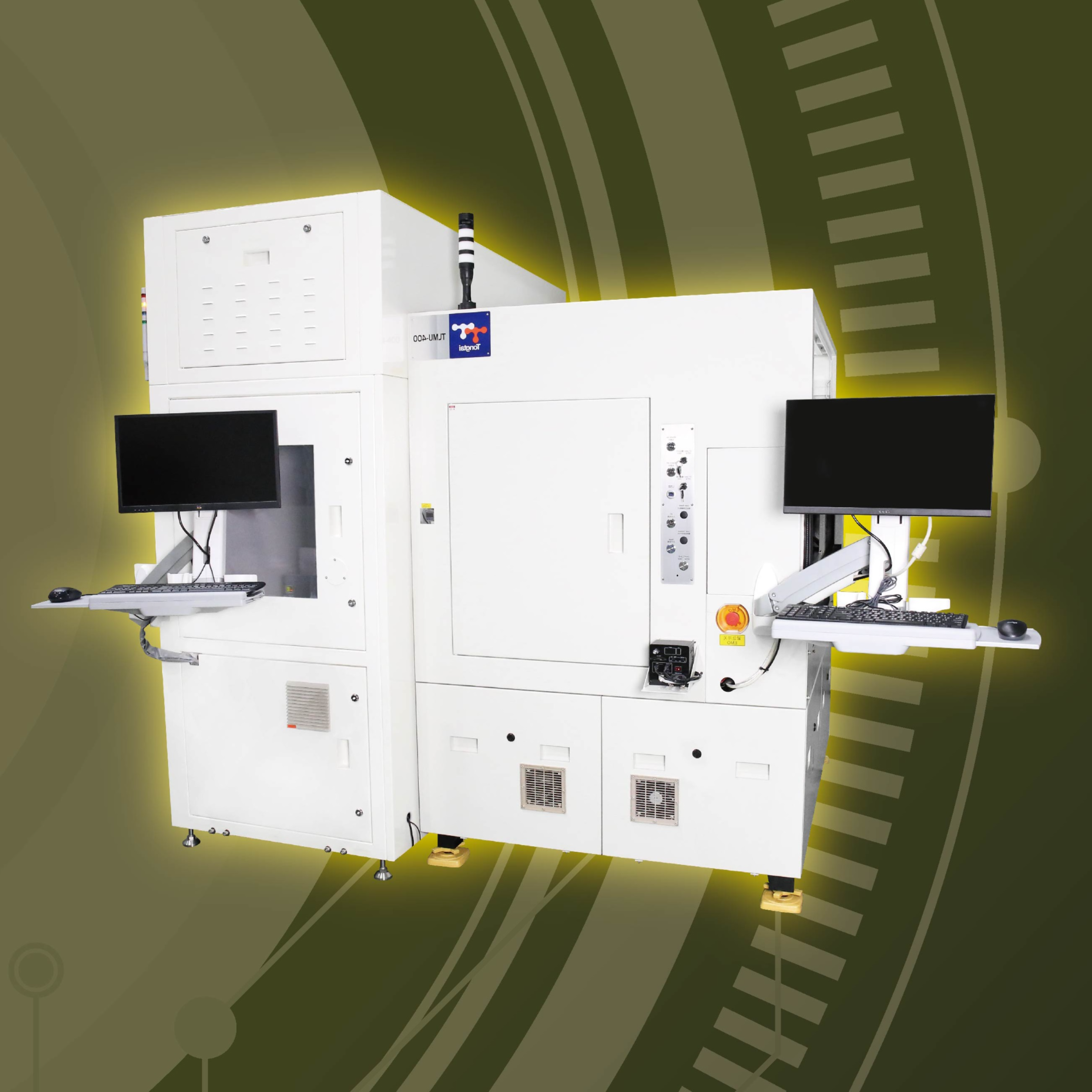
This paper describes the outcome of a laser attack study on an Android smartphone targeting specifically the secure boot sequence. Laser fault injection has become a classical attack path in the secure chip industry to investigate potential security mitigation. The implementation of such attacks on a recent mobile phone remains relatively unexplored and represents different challenges, both at hardware and software levels. In this paper, we show how the device is crafted to get a direct access to the silicon and explain the corresponding experimental setup. By inserting our own software into the boot sequence, it was possible to achieve a fine characterization of the die sensitivity to light. With the knowledge of potential perturbations, it was possible to build an attack scenario allowing to malevolently get the highest level of privilege within the mobile phone.
打开失败或需在电脑查看,请在电脑上的资料中心栏目,点击"我的下载"。建议使用手机自带浏览器。
下载该资料的还下载了
推荐学习更多>>
- 注意:
- 1、下载文件需消耗流量,最好在wifi的环境中下载,如果使用3G、4G下载,请注意文件大小。
- 2、下载的文件一般是pdf、word文件,下载后如不能直接浏览,可到应用商店中下载相应的阅读器APP。
- 3、下载的文件如需解压缩,如果手机没有安装解压缩软件,可到应用商店中下载相应的解压缩APP。